PsiPhon for Android is giving a lot of talk lately, since almost everyone says that it is one of the best applications that exist to be able to browse anonymously.
PsiPhon is an application that combines different technologies in order to obtain or hide the IP address of the person who is browsing the Internet. These technologies allow browsing anonymously, without leaving any type of trace.
This application is so well known now because since it was revealed that most governments are spying on us, more and more people are concerned about anonymity on the internet. In this way, there are many people who want to browse while keeping their private data safe.
On the other hand, cybercrime has increased a lot lately, since due to the crisis and the fact that computer applications are becoming simpler, we have more and more people attacking other people, with the aim of deleting their data and stealing information.
It really is as simple as looking for a YouTube tutorial one afternoon and getting your computer on public Wi-Fi to scan network packets. For this reason, what we have to do is try to protect ourselves on these networks, something that this PsiPhon application is capable of doing almost perfectly.
If you want to learn how to download this application in order to enjoy 100% anonymous browsing, you are in the right place, because today you will learn how to do it the right way, so that you can be safe from all Internet attackers.
Instructions for PsiPhon for Android – Download and Tips
- Download:
The first thing we are going to learn about this application is how we can download it directly to our Android phone, in order to perform its functions correctly as soon as possible. The best way that we are going to have to download it is through the Google Play Store, since as I always say, this is the best download service for Android that there is right now, either for security reasons, for privacy reasons and for speed reasons. What you have to do is search for PsiPhon in the application’s search engine, so that in this way we can easily find the application available for direct download within it. - Operation:
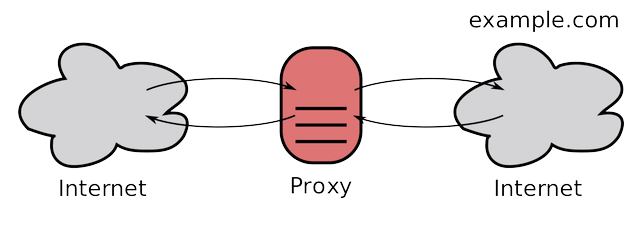
The operation of the application is quite simplified, since what we have to do is open the application and configure it so that it works and filters the content. Let’s say this application performs several functions, which are as follows. First of all, it tries to hide your IP address with a proxy server, which offers a fake IP to the server, making it believe that you are someone else. Secondly, it tries to filter all the network packets through a kind of tunnel, something that it will do so that they go through a safe place and are safe from attacks by other people. It also improves the security of Internet browsing, preventing the use of malicious scripts that could compromise your browsing security. - Uses:
Now that we know a little about what this application does, it is time to know the use it has, since it is very nice to say that this application is used for certain things, but it is not so nice to say exactly what the application is utility that it really has, something that we are going to discover right now. We have really found many utilities, the three most important utilities being the following:- Anonymity:
The first utility that we are going to have and one of the most obvious is anonymity, since most of the people who download this application is to be able to surf the Internet without being detected. It achieves this thanks to a set of everything, since the proxy server is capable of hiding the information and the tunnel is capable of preventing it from being scanned. This can be useful for people who want to browse anonymously, to avoid the control of governments and all kinds of entities on the network. - Protection:
Now it is the turn of protection, which is also important, even more than anonymity in many cases. Imagine that you are browsing the internet on a public Wi-Fi network and for whatever reason, you have to access important data. This can be a problem, for this reason, you will have to protect yourself to prevent someone from scanning your data and stealing your important data. This application achieves this thanks to the tunnel, which prevents the data from passing through the same place as the attacker’s, making you safe. - Others:
It goes without saying that this application is also used for criminal purposes, that is, by people who want to be anonymous for some reason that is beyond the law, such as having anonymity to steal bank accounts. We warn that this article is merely informative, so we are not responsible for the misuse of this application.
- Anonymity:
- Alternatives:
Although this application is very good and we have absolutely nothing against them, it also has many alternatives, which often cause us to get the same functions that this application has, but with other applications that are similar. We are going to see right now the three ways to imitate what this application does and see the main applications that apply it.- Proxy:
The first option of all that we have is to use a Proxy server, that is, a special server that is responsible for filtering the IP addressand making the system believe that you are on another site. There are many applications that do this function, although obviously some are better than others. From experience I tell you that if you want a totally anonymous proxy, your thing is to acquire your own paid proxy, since in this way, you will be able to browse 100% anonymously, since no one else will have that location or share that server., preventing third parties from tracking you for clues. - VPN:
A VPN is a virtual private network as its acronym says. ITS way of working is quite simple,that is to say, what it really does is pass the packets of a network through which you circulate through a kind of filter, which goes out to the Internet in another way: Let’s say it’s like a kind hiding place that is just outside the router, which serves to hide your IP address from the outside in an easy way and so you can easily maintain anonymity. - Tor:
Last but not least, we have the famous Tor network, one of the most secure networks in existence. This network uses the so-called onion router, which is a special router that camouflages a person’s address using a proxy and a system that moves packages zig zag, moving from one place to another instead of going all at once. This confuses the tracker and makes you completely anonymous, so it’s a good option for browsing anonymously. Also, if you are in tor you will be able to access the content of the deep web, which is hidden from the outside and is only accessible from an application such as orbot.
- Proxy: